How to view academic journal articles off campus using your library's proxy
- January 7, 2017
If you are a student or researcher, you are probably aware that much of the academic research out there is not free to access. However, if you’re affiliated with a university, you may also notice that you can access academic journals and similar content without any effort when you’re connected to your institution’s WiFi.
Suddenly, at home, the journal websites complain that you need to pay up to see the content. Chances are, though, that you can use your library’s proxy to see it.
Read MoreHow to opt out of ad tracking online: A complete guide
- July 24, 2014
We often talk about privacy here at Getting Things Tech and one of the things we are talking about when we say privacy is the massive data collection that goes on as a means to sell more effective advertising. There are pros and cons to this and we generally consent because we are assured that it lets things stay free.
However, when we know the extent to which the NSA and other intelligence organizations are gaining access to any stores of data, it might just make sense to disallow anyone from gathering personal information online, even if it is “just” to target you with ads.
Read MoreMyPermissions shows you who has access to your social media accounts
- April 19, 2014

We often will use one of our social media accounts–Facebook, Google, Twitter–to sign on another site. As you do this, there are a few permissions you have to grant along the way. In our haste, we tend to just breeze through them. After years of doing this, it is pretty easy to lose track of just who it is we have allowed to view, alter, and gather our social media data. MyPermissions puts you back in control.
Read MoreVideo: How to set up Firefox to protect your privacy and security
- March 30, 2014
Our latest video tutorial is all about how to configure a browser that many of you already are familiar with and use in a way that makes you safer online.
Read MoreHow to secure your passwords with LastPass
- March 22, 2014

A lot of our privacy and security content makes an important assumption. That assumption is that nobody can get into your account without breaking through some sort of protective measures, meaning you are only vulnerable due to either your activities or security holes on the web. The truth is, though, bad passwords are much more often your personal security’s weakest link.
Read MoreZotero, the free citation manager for students, teachers, and more
- March 3, 2014
Citing sources is one of the most tedious parts of research, academic or otherwise. You’ve done the legwork, but proving it to your readers seems to take more effort than the writing and searching! Once upon a time, websites like EasyBib or Citation Machine were the cutting edge for people trying to expedite the process. With the advent of a widely available, free citation manager like Zotero, those seem like things of the past.
Read MoreHow to use Pocket to keep track of news, articles, and more on the web
- February 27, 2014
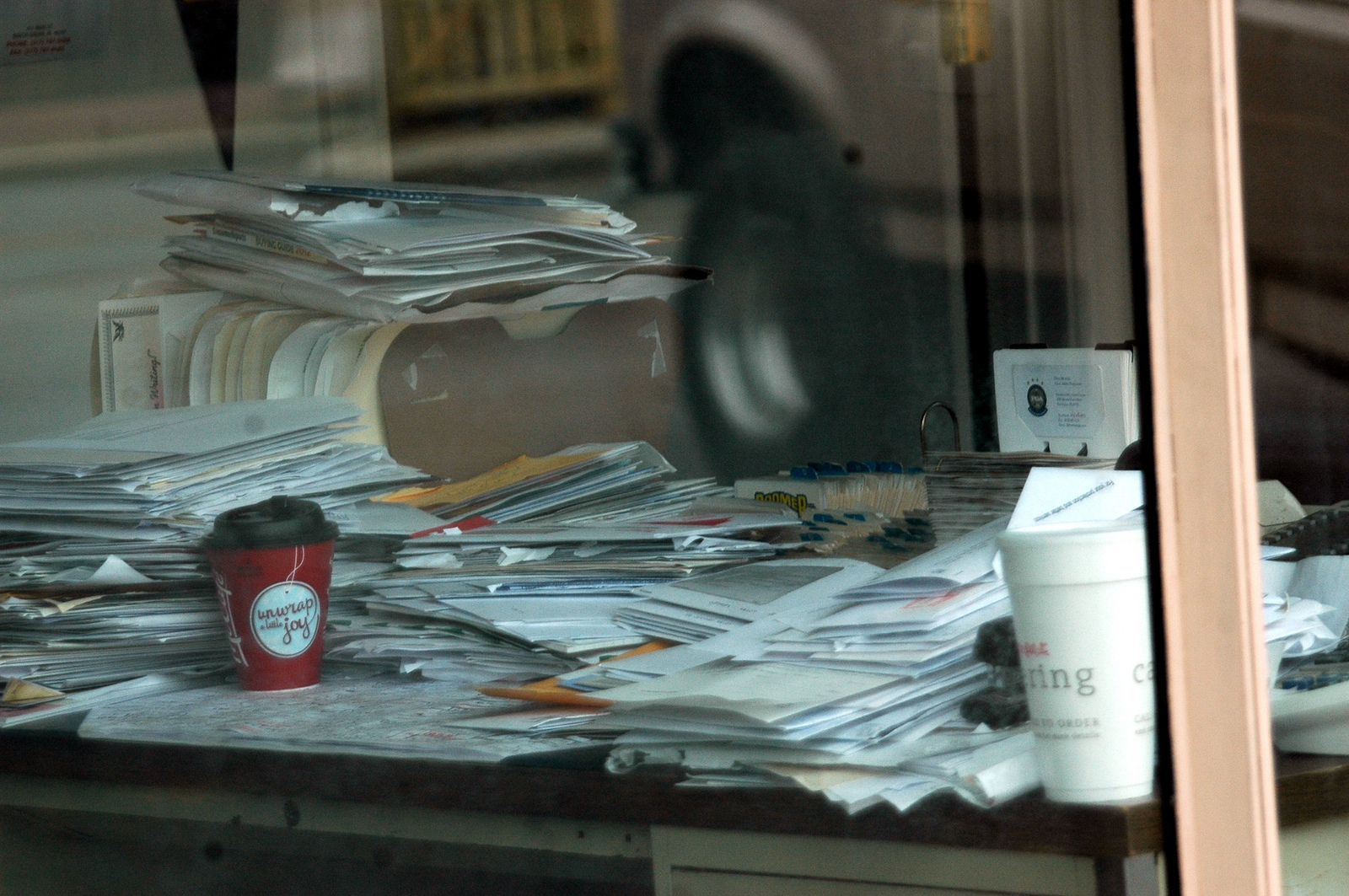
Chances are that you have seen or heard of Pocket (formerly known as Read it Later). Maybe you have just noticed its logo when you see sharing options on different websites, like this one, or you might have heard of it but you aren’t sure how it might fit into your workflow.
Today, GettingThingsTech will show you exactly what Pocket is all about. It starts with giving you a way to manage the real or virtual piling up of all those things you wanted to read.
Read MoreSearch
Recent Posts
- Make Prism.js show line numbers by default (without CSS classes)
- Hemingway App 3.0 update review: A gimmick becomes a real app
- Hugo vs. WordPress page load speed comparison: Hugo leaves WordPress in its dust
- Hemingway App 2.0 update: A worthwhile update comes with unfortunate price hike
- How to view academic journal articles off campus using your library's proxy
categories
Support This Site
Bitcoin Donations:18DP9TGdPN5usTKMRMfPk6Q2mSr4mAz8NJLitecoin Donations:
LPKQbDPykwjXr5NbXfVVQH9TqM5C497A16